Open banking has changed how money info is shared, yet it brings big safety risks. At the heart of keeping these data swaps safe are key exchange ways - the tech hello that keeps important info secret. Here's what you should know:
- Key Exchange Basic Info: These ways set up safe chats between banks and other apps using codes. Well-known types are RSA, DHE, and ECDHE, each with its own good and bad points.
- Open Banking APIs: APIs let banks and tech money areas share data well, but only if the user says yes and there are strong safety steps.
- Kinds of Encryption: Fast shared encryption (but needs safe key sharing) and stronger solo encryption (better for first swaps) are mostly used together for top work and safety.
- Rules & Safety Musts: Laws like PSD2 in Europe and CFPB rules in the U.S. need strong code, checks often, and watch all the time to stop data loss.
- What's Coming: With new fast computers coming, banks are looking into new code that can fight future risks.
Key exchange tech is key to keeping money data safe while letting new open banking ways grow. By using cool code ways, banks and tech money can make safe, easy-to-use places that make users trust them.
Best Practices for Securing Open Banking and Financial APIs with Keycloak

Main Ways to Swap Keys in Open Banking
Open banking uses a few safe ways to set up safe links between banks and money sites. These ways keep the money data safe, making sure only allowed apps can get the info they need. Each way fits different cases, each with its own strong points.
Key Swap Rules for Codes
Three main rules make sure talks are safe in open banking: RSA, DHE, and ECDHE.
RSA Key Swap: This way uses a pair of keys: one public, one private. The bank gives out a public key that the client uses to lock a top secret. Only the bank's private key can open this to get session keys. RSA counts on the hard job of splitting big numbers for safety, but it has a big flaw: it does not keep past secrets safe. If the bank's private key gets out, old talks could be seen.
Diffie-Hellman Ephemeral (DHE): DHE fixes this by making new key pairs for each chat. Each side makes a short-term private value and shares public ones. By mixing their private value with the other side's public value, both sides make a shared secret on their own. This makes sure that if one chat gets hit, others are still safe.
Elliptic Curve Diffie-Hellman Ephemeral (ECDHE): ECDHE works like DHE but uses curve math. This lets it be just as safe with smaller keys, making it quick and fit for use. ECDHE is good for mobile banking, so it's a top pick in new open banking systems.
These code ways are made even stronger by OAuth 2.0, which adds more safety with token-based OKs.
OAuth 2.0 and Token-Based Safety
While code rules keep chat lines safe, OAuth 2.0 handles who can do what, making sure sites can get to your bank info safely. For example, when you let an app like Mezzi in, OAuth 2.0 makes time-limited access tokens. These tokens work like short term digital keys, giving some rights for a little while. After they check who you are and that you agree, the bank gives out these tokens, which the money site uses to ask for your info.
The safe lines set by key swap rules keep these tokens from being taken or changed. Also, tokens can be made to stop after some time, and banks can stop them right away if they see fishy acts. This way, both safe and checked use of your money info is made sure.
To make data moves even safer, open banking systems use both the same and different key codes.
Same vs. Different Key Codes
Both same and different key codes help keep data safe when moving it, each in its own way.
Same Key Encryption: This way uses one key to lock and unlock data. Its speed and smooth work make it best for handling lots of deal info. But making sure the shared key is safe and well held can be hard.
Asymmetric Encryption: This way uses two keys that link through math - a public key to lock data and a private key to unlock it. Since anyone can have the public key, money sites can lock their data without the risk of sharing a secret key. This gets rid of the key-sharing issue found in symmetric encryption.
Hybrid Encryption Model: Open banking often mixes the best of both ways. Asymmetric encryption sets up a shared secret, while symmetric encryption takes care of sending the real data. This mixed plan keeps it safe and fast, which is key for sites that collect data from many money groups.
| Aspect | Symmetric Encryption | Asymmetric Encryption |
|---|---|---|
| Key Usage | One key for both lock and unlock | Two keys: open key for lock, secret key for unlock |
| Speed | Quick; good for a lot of data | Slower; uses more power |
| Security | Safe if key is kept hidden | Better safe at the start of key swap |
| Best Use | Live deals, moving much data | Proving who you are, safe links |
| Key Sharing | Must share key in a safe way | Open key can be told to all |
On sites like Mezzi, which pull data from many banks, this mixed way to lock info makes sure your bank details stay safe. It also lets them update your money board in real time. The system takes care of the hard stuff like key trades and locking info by itself. This means you get easy and safe entry to all your money data in one place.
Rules and Safety Needs
Bank rules and safety steps are key in shaping how exchanges work within open bank systems. These rules make sure all money platforms follow the same safety acts, keeping money data safe.
Open Banking Musts
Area rules build the base for safety in open banking. In Europe, the Payment Services Directive 2 (PSD2) asks for strong user checks and safe talk ways. In the United States, money groups must stick to Consumer Financial Protection Bureau (CFPB) guides and the Gramm-Leach-Bliley Act, while the Federal Financial Institutions Examination Council (FFIEC) offers extra help on checks and entry controls.
Some key must-do things include:
- Using Transport Layer Security (TLS) 1.2 or more for all data moves.
- Setting up strong cert check steps.
- Keeping full logs of all entry tries for check aims.
- Doing regular safety checks and updating key swap ways to face new risks.
These rules help shape how banks deal with keys and certs, making sure they keep up with top safety acts.
Key Handling and Cert Moves
Handling digital certs right is key for safe talks. Cert check is a fast step, looking for trust by checking the source, end dates, and cancel status. Regular key changes are also key - long-term keys are often changed every 12 to 24 months, while session keys might shift every few hours. If a cert is at risk, tools like Certificate Revocation Lists (CRLs) and the Online Certificate Status Protocol (OCSP) can kill it quick.
For key safe spots, banks use Hardware Security Modules (HSMs) that meet FIPS 140-2 Level 3 rules. These safe tools break keys if safety is hurt, adding more safety.
Data Aggregator Safety Jobs
Data helpers, making safe links between money groups, hold big safety jobs. Each group’s link needs its own lock key, keeping it alone and in line with set bank safety steps. For example, a spot like Mezzi may handle many safe links at once, each with its own key.
To meet rule needs, helpers must:
- Keep full check logs of every data reach and key swap.
- Go through usual third-party safety checks and test attacks.
- Stick to data small rules, reaching only needed info (like asking for balance info without seeing deal pasts).
- Follow tell rules, which ask rule folks to know within 72 hours and customers told right away.
These mixed rules build a strong safety way, making sure that banks, third-party folks, and data helpers work as one to keep money info safe across linked systems and areas.
sbb-itb-e429e5c
Key Swap in Money Account Link Systems
Many account systems have the hard job of keeping user info safe while also linking to different banks and groups. They do this by using strong key swap ways, which keep many-account links safe and protect info as it flows.
Safe Link of Many Accounts
When linking to lots of money accounts, systems set up safe, coded paths for each link. This means that if one link is not safe, others are still fine. To make it even safer, each path gets its own code key that changes often. This style makes sure each account stays alone and safe.
Full Coding for Keeping Data Safe
Along with keeping each account link safe, systems use many layers of end-to-end coding to fully protect data. This keeps data coded not only when moving but also when stored and during real-time talks. Adding to past key swap ways, this many-layer coding offers strong safety.
Key control is very important in this process. Systems must safely take care of every part of a key's life - making, keeping, giving out, using, changing, and finally ending or taking back the key. Fine control inside the key control system makes sure certain keys open certain files, putting in more safety. Also, digital signs and Message Codes keep data true and real in all linked accounts.
How Mezzi Uses Key Swap Ways
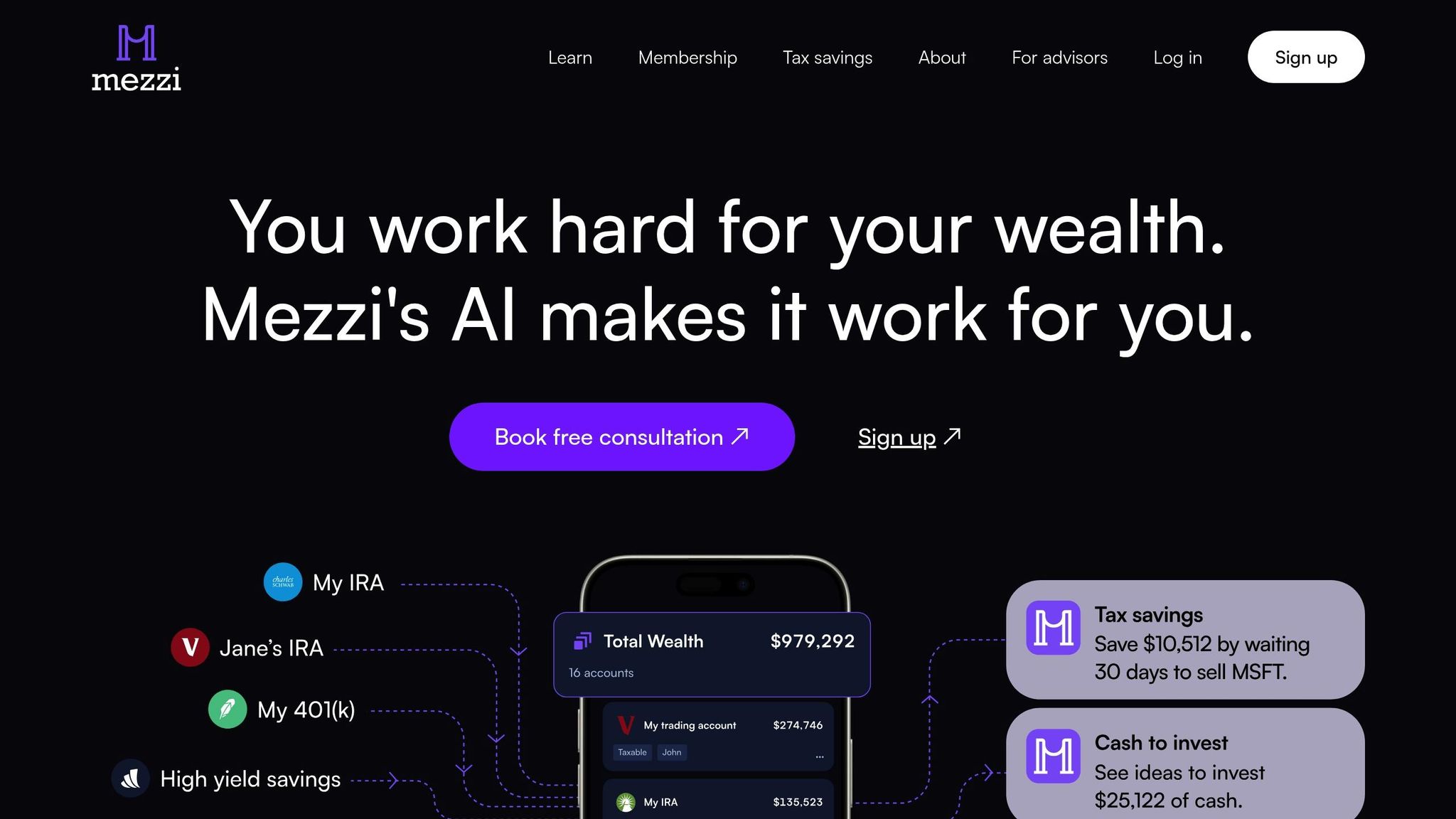
Mezzi uses common coding rules and auto key rules, working with helpers like Plaid and Finicity. These helpers handle the complex key swap jobs across many money groups, letting Mezzi focus on keeping user info safe in its own space.
To meet rules and set standards, Mezzi watches all the time and uses fine controls. For users with many accounts - like stock, retirement, and bank accounts - Mezzi makes alone coded paths for each group. This not only lets the system's AI look at a user’s whole money scene but also keeps each link safe. For instance, the X-Ray tool can find hidden stock ties across accounts without risking the safety of any one link.
Plus, key swap ways help Mezzi's live skills. When giving AI-driven tips, like tax saving ways, the system uses new account info through safe, checked paths. These paths update on their own, making sure the user's experience is smooth and safe.
Benefits and Challenges of Key Exchange in Open Banking
Key swap set-ups are key in open banking, bringing big safety ups and tough to do tasks. These steps are key to keep safe that need to know stuff, but they also need careful work and smart moves to keep safe while still running smooth.
Ups vs. Tough parts
Good key swap systems have many good points like many layer lock-up, finding dangers early on, and keeping data safe when sent. They also help with rules, build trust, and make things like stopping access right away easy with key lists.
But putting these systems in place isn't easy. Hard stuff like changing keys often, keeping track of certs, and safe keeping places need deep know-how. Also, mixing with many money places often makes for fit problems, as each one may have its own safe steps and rules.
How fast things run can also drop. Locking up info, safe meet-ups, and checking tokens - while must-do - can slow getting and using data, which might change how well the user's stuff works.
| Part | Good Things | Hard Parts |
|---|---|---|
| Security | Many encryption layers, safe send of data | Hard to set up, always need to fix, need experts |
| Compliance | Follows rules, clear records, less legal trouble | Rules change a lot, rules differ for each place, lots of checks |
| User Experience | More trust, easy to see and use controls, can stop access quickly | Might slow down, hard to fix errors, need to solve tech issues |
| Scalability | Safe to mix many accounts, makes things run by self | Takes lots of resources, not always fits well, costs a lot for setup |
Key swap plans cut long-time risks of breaks, but they start with high early and keep-up costs. Jobs like key change, permit updates, and match tests need steady watch and full-on help. These work needs make smooth mistake fix big for dealing with fails without stopping data use.
Even with the hard parts, the need for strong key swap ways is on the rise. With more safety risks and tight rules, these plans are now a must. Places that tackle these hard parts well not only make their safety better but also get ahead by making users trust them more. By putting tough plans first, even the most tricky set-ups can stay safe in the fast-change world of open bank work.
New Changes in Bank Safety
The field of bank safety is changing a lot. It blends old ways with new ideas. As tech grows and rules shift, banks are looking for new ways to keep data safe. They are now focusing on using advanced key sharing methods, especially with the rise of threats like quantum computing.
New Key Sharing Tech
A big step in this area is post-quantum cryptography. With quantum computers close, old ways to lock data may not work soon, putting bank data at risk. To fight this, banks are trying out new, quantum-safe steps. These steps use hard math problems that quantum computers can't solve. But changing to these new, safe steps needs a lot of planning to make sure they work with old systems.
Changes in rules are also key in picking up these new techs. As rule-makers update their secure data sharing rules, banks will need to use quantum-safe ways more. These new rules aim to make a safer space for open banking and push for better safety ways.
The big task now is to find a good mix of strong safety and easy use. By using new cryptography methods and keeping up with new rules, the future of bank safety could be both very safe and easy to use.
FAQs
How does OAuth 2.0 keep bank data safe through APIs?
OAuth 2.0 is a well-known setup that helps lock banking APIs. It gives out rights to user accounts but does not ask for key details like passwords. It uses secure tokens which allow short-term access.
This way of using tokens cuts the risk of entry without permission and lets money systems and other apps talk well. By using set rules from the field, OAuth 2.0 makes sure money info stays safe.
How are open banking systems dealing with the safety threats of quantum computing?
Open banking systems are taking on the security issues from quantum computing by making quantum-proof security steps. These steps are made to keep safe important money details from the big power that coming quantum computers may have, which might break current ways to keep data safe.
In the U.S., banks and those who make the rules are working to make cybersecurity better. By putting in place stronger safety steps now, they want to stay ahead of future dangers, making sure that money data is safe even as tech moves forward. This way of thinking ahead helps keep the sharing of money details safe in a fast-moving digital world.
Related Blog Posts
Table of Contents
Book Free Consultation
Walk through Mezzi with our team, review your current situation, and ask any questions you may have.
